
7 Possible Security Testing Mistakes that Can Occur Anytime
May 18th, 2017
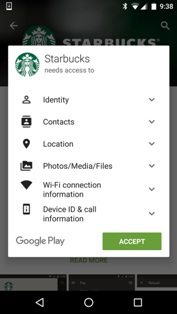
Mobile apps become a double- edged sword especially when a mobile payment application has to do mass transfers. New features are prone to hacking and extortion if not handled with care. NowSecure Mobile Security Report 2016 has found that 25% of the mobile applications always deal with at-least one highly extended security risk. When attacks on mobile applications increased, authorities started considering security checks before launching the app.
 Here, we are going to discuss about 7 possible security testing errors that may occur but can be avoided:
Here, we are going to discuss about 7 possible security testing errors that may occur but can be avoided:
 We just can't do anything about it.
But!
A critical action plan can be implemented by:-
1. Monitoring the device, identifying every unusual activity
2. Appointing an in/out house team to identify and recover threats
3. Having policies that help you to limit the damages
We just can't do anything about it.
But!
A critical action plan can be implemented by:-
1. Monitoring the device, identifying every unusual activity
2. Appointing an in/out house team to identify and recover threats
3. Having policies that help you to limit the damages
 Here, we are going to discuss about 7 possible security testing errors that may occur but can be avoided:
Here, we are going to discuss about 7 possible security testing errors that may occur but can be avoided:
- Failing to understand how an application is exposed to risk
- Failing to connect security with application design
- Lacking the quality in security testing
- Use end-end encryption in data
- Exposing sensitive data
- Limit app features
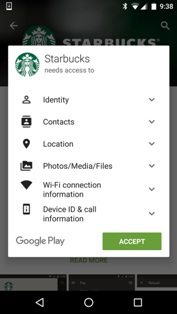
- Develop a security response plan
 We just can't do anything about it.
But!
A critical action plan can be implemented by:-
1. Monitoring the device, identifying every unusual activity
2. Appointing an in/out house team to identify and recover threats
3. Having policies that help you to limit the damages
We just can't do anything about it.
But!
A critical action plan can be implemented by:-
1. Monitoring the device, identifying every unusual activity
2. Appointing an in/out house team to identify and recover threats
3. Having policies that help you to limit the damages

 Mobile App Testing
Mobile App Testing Web App Testing
Web App Testing Game Testing
Game Testing Automation Testing
Automation Testing Security Testing
Security Testing Performance Testing
Performance Testing Selenium
Selenium Test Management
Test Management Usability Testing
Usability Testing Guides and Tutorials
Guides and Tutorials Expert Insights
Expert Insights Software Testing Events
Software Testing Events Load Testing
Load Testing Performance Testing
Performance Testing Hire a Tester
Hire a Tester





