
12 Disastrous Software failure that created chaos0
April 23rd, 2018
The word ‘Disaster’ is an underplaying word for any organization or brand that had incurred losses due to software failure. Though technology and innovative applications have made life much simpler, numerous software bug instances are recorded by organizations.
Since it’s a human tendency to make mistakes and software products are coded and tested by humans, every piece of software, therefore, has some of the other glitches. In this run, let us look at 12 infamous epic software bugs that have changed the way developers and testers develop and test any software application.
1. Data breach at Yahoo – August 2013
An epic and historic data breach that occurred at Yahoo in August 2013 affected almost 3 billion users was hacked by a group of professional black hats from Eastern Europe. The hackers were also suspected of stealing and selling customer information hacked from LinkedIn, Myspace and Tumblr.
Similarly, there again occurred a breach in 2014 which affected 500 million Yahoo users but was different from the 2013 incident. People using Yahoo services should always follow proper hygiene by using two-factor authentication and not using the same password for a long period.
2. HSBC Online Banking Failure- April 2016
One of the world’s leading banks, HSBC, suffered an IT outage that left thousands of customers stranded. On 4th January 2016, people started facing problems while logging into the online and mobile banking services. The problem continues for the next 2 days and people feared to lose their money due to the failed system.
Though, HSBC released an official statement on Twitter apologizing for the audience for the technical issue. Though HSBC never came up with the exact reason for this downtime, we are sure it was caused due to some technical breaches.
3. North American Blackout- August 2003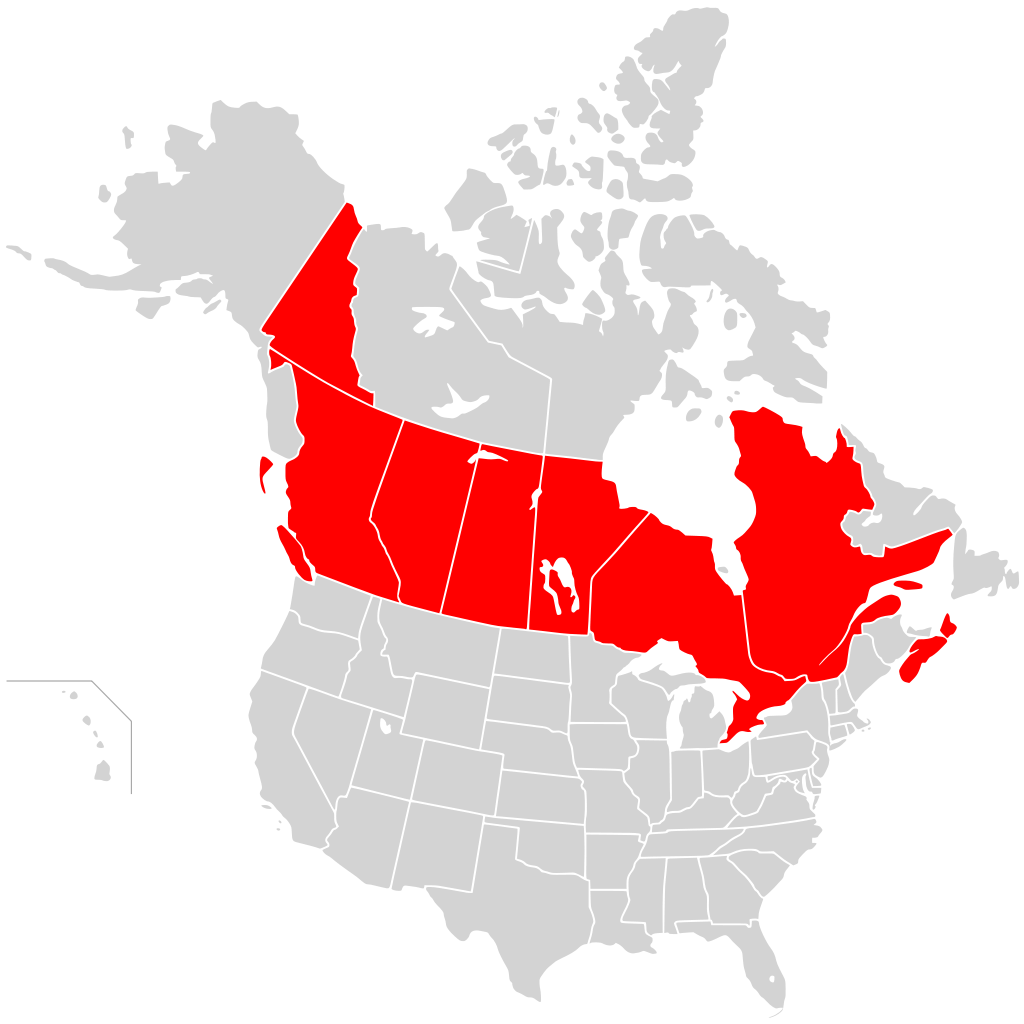
On August 14, 2003, more than 50 million people lost power due to an aging grid that encountered a series of technological flaws, stretching from New York City to Ohio. The problem started when a power plant along the southern shore of Lake Erie, Ohio went offline due to the high demand which put the rest of the power network under greater stress.
While you might think that this has got nothing to do with a software bug, but the incident could have been avoided if the software that triggered the alarm system had not been bugged. The alarm could have alerted the officials at the right time to averting the incident.
4. ARIANE 5 Failure
On 4th June 1995, Europe’s newest satellite-launching rocket, ARIANE 5 ended in failure. Just after 40 seconds of it taking off, the launcher broke down and exploded. According to the team that investigated the failure, the destruction occurred due to the 64-bit number being coded into a 16-bit space. The loss of information was due to the error in the specification and design of the inertial reference system.
5. Pentium FDIV Bug- Nov 1994Chips are like the brain for every electronic device. In 1994, the CPU market leader Pentium found that their chip simply couldn’t perform its math. Pentium tried and tested to find out that no matter what software changes you perform, the results stood the same being inaccurate for all combinations. The problem actually was the faulty math co-processor that was known as the floating-point unit.
When the floating-point unit accessed any empty cells in the algorithms, it would show a zero response instead of real calculations. The company was lucky in terms of finding the bug in an early stage before it shipped the chips to its customers.
6. Cisco Email Security Appliance Vulnerability- Sep 2016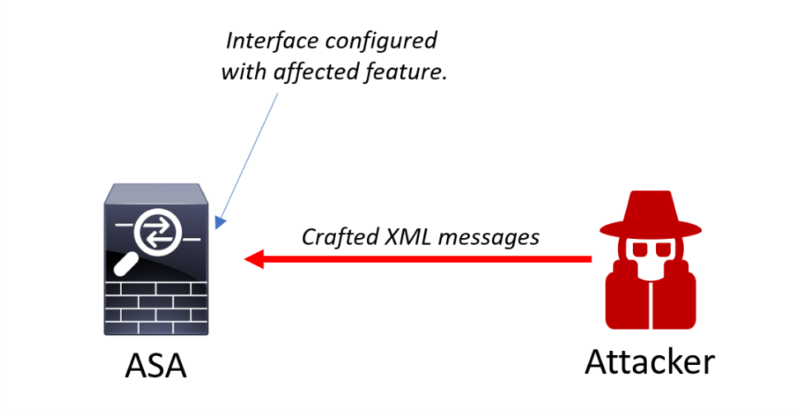
In September 2016, a deformity in the Multipurpose Internet Mail Extensions (MIME) scanner of Cisco AsyncOS Software allowed remote attackers to bypass the system. The vulnerability was due to improper handling of the MIME header in the email attachment. A successful attempt allowed the attacker to access the configured email message and content filtering that allowed the malware to be delivered to the recipient.
Seeing the bug, it is advised that customers regularly consult the Cisco representatives for products to determine the exposure and complete the upgrade solution. If the support isn’t clear, customers can contact the Cisco Technical Assistance Centre (TAC) or their maintenance providers.
7. Cyber Attack On Nuclear Power Plant – October 2016
On October 10th, 2016 the world watched a team of highly skilled hackers takes down power grids that were a result of cyber-attack. Hackers were trying to penetrate the computer network of companies that operated nuclear power stations. This shows that disturbances in nuclear infrastructure due to a Cyber Attack is not always a ‘Hollywood stunt’!
The head of the International Atomic Energy Agency (IAEA) did not disclose much of the attack that took place but said it disrupted the day to day activities at the plant.
8. WannaCry – May 2017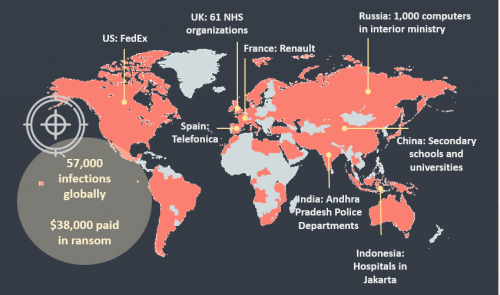
A recent software attack, WannaCry was a worldwide cyberattack that targeted co putters running Microsoft Windows operating systems. The attack encrypted files on PC’s hard drives which made them inaccessible to users. The attackers demanded a ransom bitcoin amount to decrypt the files on your system.
The attack was brought under control on May 14th, 2017 when network engineer Diaries Huss share a ‘kill switch’ names malware that eventually stopped the spread of this virus. However, later the developer of WannaCry updated his ransomware to remain unaffected by the malware.
9. Bitcoin Node Crash – April 2017
On 23rd April 2017, the world’s largest digital currency, bitcoin, came down crashing due to what appeared to be a memory leak. The software bug leads to, in effect, duplication of work, with wrong actors exploiting bugs for political points. While most of the bitcoin owners welcome an increase in the block sizes, the fact cannot be ignored that bitcoin seems very vulnerable to software bugs and attacks which needs improvements for sure.
In the end, it was all just codes, hence bugs will be found and fixed. This won’t be an issue until the bugs are relatively harmless.
10. Mariner 1's $135 Million Software Bug- July 1962A software bug that occurred due to a simple punch card is considered one of the most expensive failures in history. In 1962, the software bug; let to the destruction of Mariner 1 spacecraft even before it could complete its mission on Venus.
Just minutes before the satellite could take off, the onboard guidance antenna failed, which hindered the backup radar system guiding the spacecraft. However, later it was found that there were minor errors in the software of the guidance system which led to this huge loss.
11. The Mars Climate Orbiter- September 1999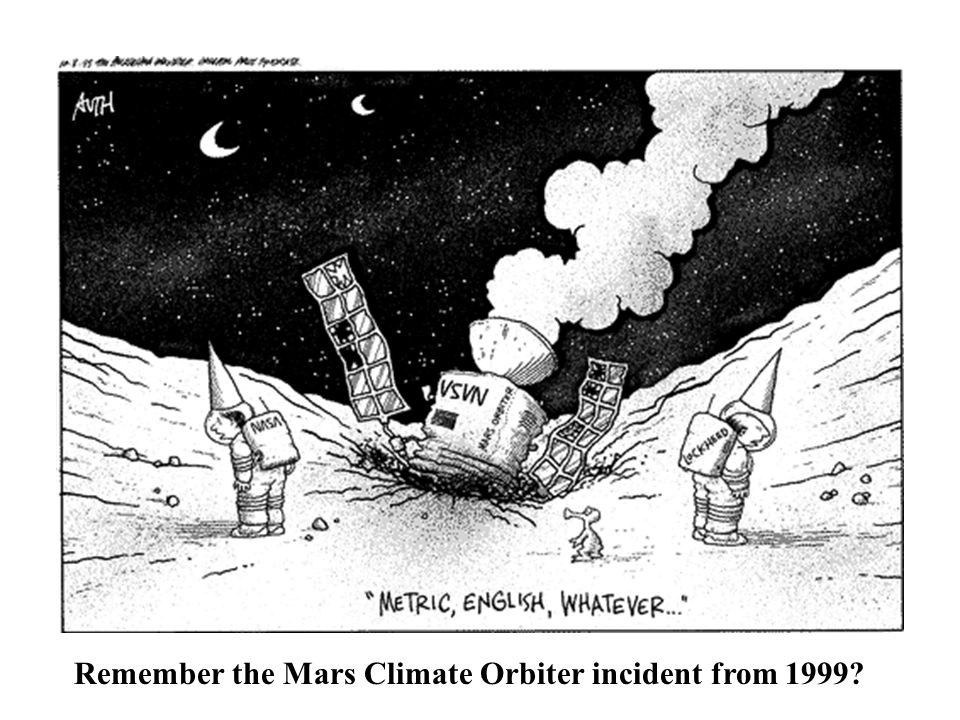
On December 11th, 1999, NASA launched the Mars Climate Orbiter to study the climate and surface changes. The ground-based software team produced an output of non-SI units (pound-seconds) rather than the metric units which uncompensated and unconverted the units causing the thrusters to be powerful to a limit the orbiter couldn’t take.
The result was that the orbiter entered the Mars atmosphere at a wrong angle rather than entering the planets orbit. It was the responsibility of the engineers to check for the computer program's compatibility.
12. The Morris Worm– November 1988
The Morris worm was one of the first worms that were introduced into computer systems with an intention being completely harmless. The program was developed by Robert Tappan Morris, who was a student at Cornell University. The worm spread across thousands of computers almost crashing systems due to coding errors. The news made the headline in no time.
The cleaning up of this mess had gone as high as around $100 million. Morris was of the thought that the worm would help improve the computer’s security features, which it did not.
Conclusion
Today, the advancements in information technology have huge resources to bring down any instances of a software bug that could affect our daily lives. But learning from history, it is important to keep a check on the software and test it to perfection with the help of an established software testing company so that you will not encounter any loss.


 Mobile App Testing
Mobile App Testing Web App Testing
Web App Testing Game Testing
Game Testing Automation Testing
Automation Testing Security Testing
Security Testing Performance Testing
Performance Testing Selenium
Selenium Test Management
Test Management Usability Testing
Usability Testing Guides and Tutorials
Guides and Tutorials Expert Insights
Expert Insights Software Testing Events
Software Testing Events Load Testing
Load Testing Performance Testing
Performance Testing Hire a Tester
Hire a Tester





