
What is gray/ grey box testing? Examples Included!
April 18th, 2019
Gray box testing/ grey box testing is a method of testing a software system – application or product, externally and internally by using a combination of "white box testing" and "black-box testing".
Gray box testing is carried out with limited or partial knowledge of the internal workings of the software system/application.
With a view to conquering the deficiencies and ambiguities found in such type of testing, Grey Box Testing (also spelled as Gray Box Testing) has been developed as a productive merger of white box and black box testing.
White Box Testing – the internal structure (code) is known
Black Box Testing – the internal structure (code) is unknown
Grey Box Testing – the internal structure (code) is partially known
let's dive dip into the implication of grey/gray box testing in software engineering.
 Grey Box Testing Methodology
First – White Box Testing to study and gain a basic understanding of the internal features of the application.
Second – Design and define test cases based on thorough knowledge and understanding to cover each and every aspect of the application.
Third – Black box testing to execute developed test cases to externally test the qualities of the software application.
Best Suited Applications:
Grey-box testing is an ideal fit for Web-based applications.
Grey-box testing is the best technique for domain or functional testing
Grey Box Testing Strategy in software engineering
It's not necessary in this methodology that source code is required by the tester to design test cases. To carry out this testing process, test cases can be designed based on the algorithm, knowledge of architectures, internal states, or other advanced descriptions of the program behavior.
It utilizes all the clear-cut techniques of black box testing for function testing. The generation of a test case is based on requirements and presetting all the conditions by the assertion method.
The standard steps to carry out Grey box Testing are as follows:
Step 1: Selection and identification of inputs from White-Box and Black-Box testing inputs.
Step 2: Identification of probable outputs from the above-selected inputs.
Step 3: Identification of all the key paths to pass through during the testing phase.
Step 4: Identification of sub-functions to carry out deep-level testing.
Step 5: Identification of inputs for sub-functions.
Step 6: Identification of likely outputs for sub-functions.
Step 7: Execution of a test case for sub-functions.
Step 8: Verification of the appropriateness of outcome.
Step 9: Repetition of Steps 4 and 8.
Step 10: Repetition of Steps 7 and 8.
Security-related, GUI-related, Database related, Browser related, and Operational system-related testing are all part of the test cases designed for the process.
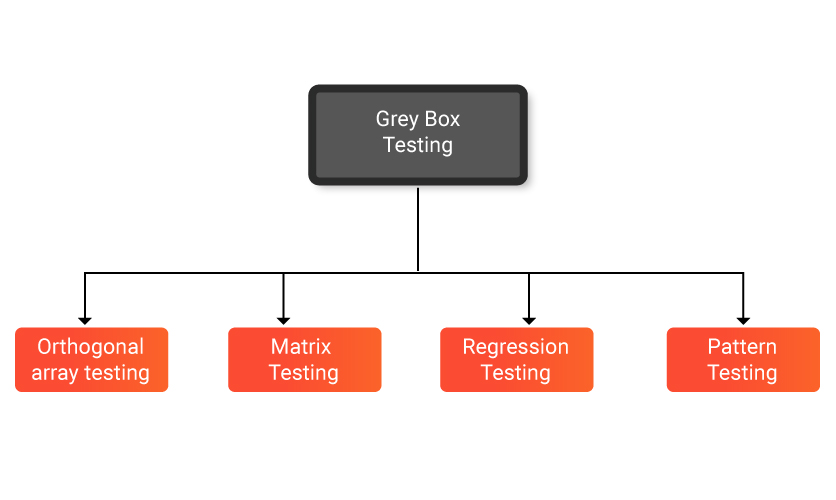
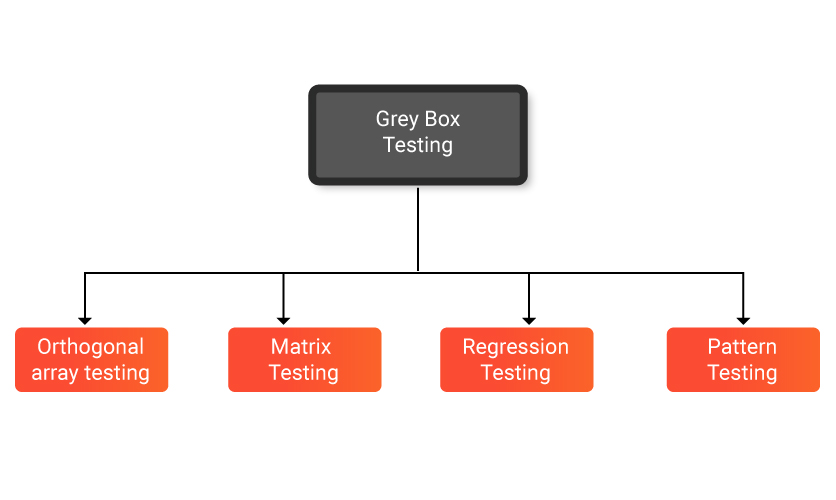
Types of Grey box testing/gray box testing/Grey box testing techniques
Matrix Testing
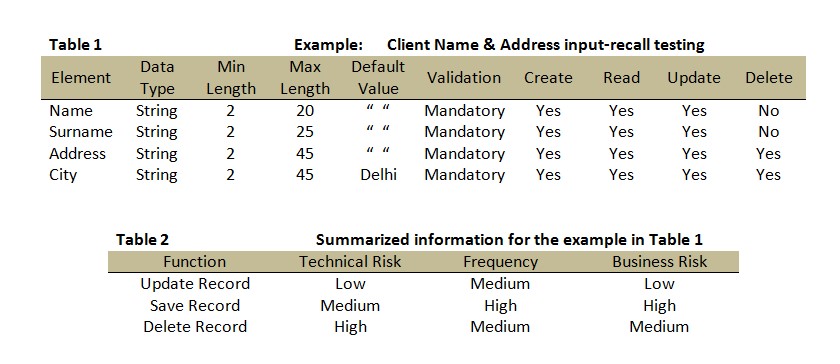
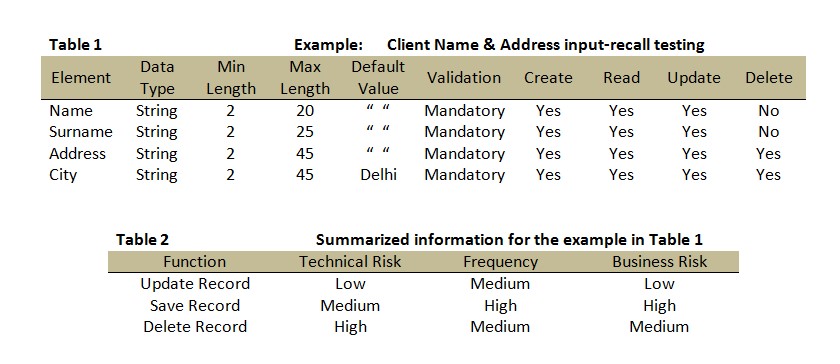
Matrix testing, a technique coming under Grey Box testing, defines all the used variables of a particular program. In any program, variables are the essential elements through which values can move through the program.
It should be on par with the requirement without which the readability of the program and speed of the software will be reduced. The matrix technique is a way to eliminate uninitialized and unused variables by identifying used variables from the program.
Examination of inherent risks like technical risks and business risks that are associated with the variables with different frequencies labeled by the software developer is carried out under this type of testing.
The design of test cases becomes smooth and easier when all of this information is summarized in two types of tables as in the following example:
Grey Box Testing Methodology
First – White Box Testing to study and gain a basic understanding of the internal features of the application.
Second – Design and define test cases based on thorough knowledge and understanding to cover each and every aspect of the application.
Third – Black box testing to execute developed test cases to externally test the qualities of the software application.
Best Suited Applications:
Grey-box testing is an ideal fit for Web-based applications.
Grey-box testing is the best technique for domain or functional testing
Grey Box Testing Strategy in software engineering
It's not necessary in this methodology that source code is required by the tester to design test cases. To carry out this testing process, test cases can be designed based on the algorithm, knowledge of architectures, internal states, or other advanced descriptions of the program behavior.
It utilizes all the clear-cut techniques of black box testing for function testing. The generation of a test case is based on requirements and presetting all the conditions by the assertion method.
The standard steps to carry out Grey box Testing are as follows:
Step 1: Selection and identification of inputs from White-Box and Black-Box testing inputs.
Step 2: Identification of probable outputs from the above-selected inputs.
Step 3: Identification of all the key paths to pass through during the testing phase.
Step 4: Identification of sub-functions to carry out deep-level testing.
Step 5: Identification of inputs for sub-functions.
Step 6: Identification of likely outputs for sub-functions.
Step 7: Execution of a test case for sub-functions.
Step 8: Verification of the appropriateness of outcome.
Step 9: Repetition of Steps 4 and 8.
Step 10: Repetition of Steps 7 and 8.
Security-related, GUI-related, Database related, Browser related, and Operational system-related testing are all part of the test cases designed for the process.
Types of Grey box testing/gray box testing/Grey box testing techniques
Matrix Testing
Matrix testing, a technique coming under Grey Box testing, defines all the used variables of a particular program. In any program, variables are the essential elements through which values can move through the program.
It should be on par with the requirement without which the readability of the program and speed of the software will be reduced. The matrix technique is a way to eliminate uninitialized and unused variables by identifying used variables from the program.
Examination of inherent risks like technical risks and business risks that are associated with the variables with different frequencies labeled by the software developer is carried out under this type of testing.
The design of test cases becomes smooth and easier when all of this information is summarized in two types of tables as in the following example:
 All Info About Grey Box Testing (With Examples)
From the information in the above two tables, the testing analyst can immediately make out that the technical and business aspect of the code, namely saving and deleting records requires testing.
Regression Testing
This type of testing is carried out after executing a functional development or repair to the program.
To verify whether the modification in any of the previous versions of the software has regressed or caused any unintended or adverse side effect in other aspects of the program in the new version, the following testing strategies can be pursued:
All Info About Grey Box Testing (With Examples)
From the information in the above two tables, the testing analyst can immediately make out that the technical and business aspect of the code, namely saving and deleting records requires testing.
Regression Testing
This type of testing is carried out after executing a functional development or repair to the program.
To verify whether the modification in any of the previous versions of the software has regressed or caused any unintended or adverse side effect in other aspects of the program in the new version, the following testing strategies can be pursued:
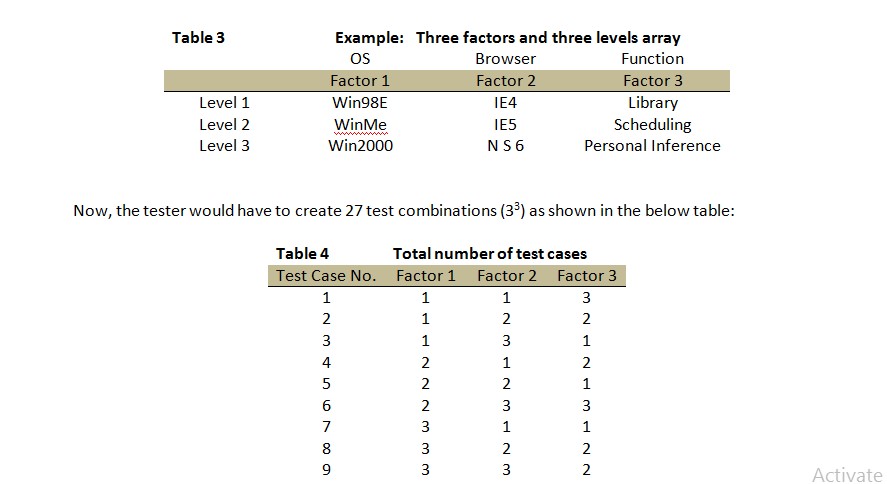 By conveying values for each factor and then, of course, extrapolating for combined pairing, the total number of test cases will surely come down to nine from 27.
Though simple, this effective technique helps in maximizing the required testing coverage.
Pattern Testing
This testing is carried out by using the record of analysis on the historical data of the previous system defects. These analyses may contain specific reasons for the defect or bug with information on the problem that has been addressed, applicable situation, generic test cases, etc.
Unlike black box testing, grey box testing plows within the code to determine the reason for the failure so that they can be fixed in the next software. It is noteworthy that pattern testing is applicable only to such type of software that has been developed by following the same pattern of previous software as the possibility of similar defects occurs in this software only.
Generally, the Grey box methodology employs automated software testing tools to conduct the testing. Module drivers and stubs are created to relieve the tester from manually generating the code.
Examples for grey/gray box testing
Grey Box Testing is said to be performed when –
By conveying values for each factor and then, of course, extrapolating for combined pairing, the total number of test cases will surely come down to nine from 27.
Though simple, this effective technique helps in maximizing the required testing coverage.
Pattern Testing
This testing is carried out by using the record of analysis on the historical data of the previous system defects. These analyses may contain specific reasons for the defect or bug with information on the problem that has been addressed, applicable situation, generic test cases, etc.
Unlike black box testing, grey box testing plows within the code to determine the reason for the failure so that they can be fixed in the next software. It is noteworthy that pattern testing is applicable only to such type of software that has been developed by following the same pattern of previous software as the possibility of similar defects occurs in this software only.
Generally, the Grey box methodology employs automated software testing tools to conduct the testing. Module drivers and stubs are created to relieve the tester from manually generating the code.
Examples for grey/gray box testing
Grey Box Testing is said to be performed when –
 Objectives of Grey Box Testing
Some of the main objectives are:
Objectives of Grey Box Testing
Some of the main objectives are:
 Conclusion
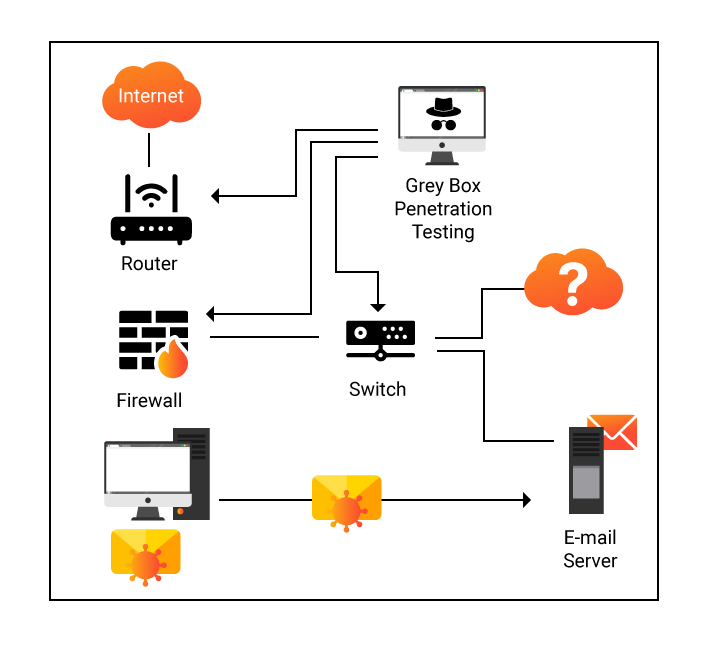
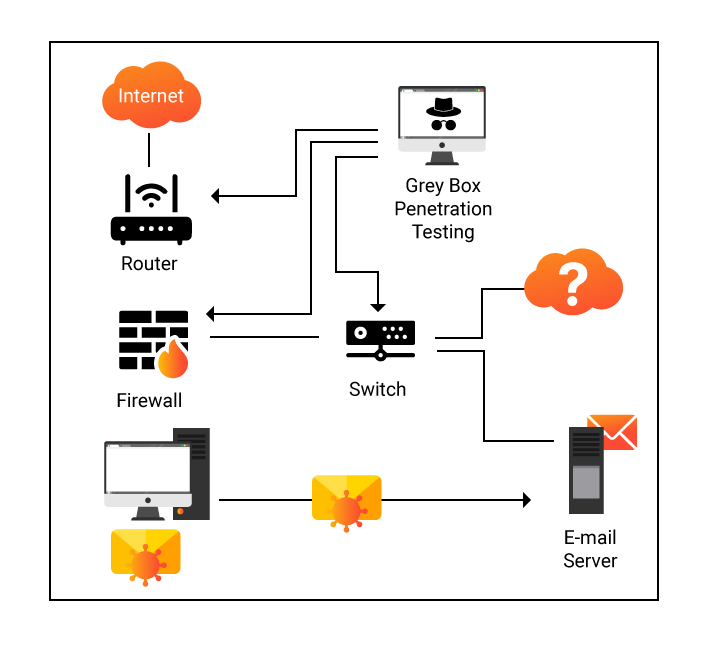
Nowadays in this modern world, nobody is indisputably safe from cybercrime irrespective of whether it is a big corporate or an individual, government organization, or non-benefit association.
The potentiality of becoming a cybercrime target looms large. Grey box testing comes up as a priceless tool for securing security in software. Significant vulnerabilities can be uncovered by giving in less effort and cost.
Conclusion
Nowadays in this modern world, nobody is indisputably safe from cybercrime irrespective of whether it is a big corporate or an individual, government organization, or non-benefit association.
The potentiality of becoming a cybercrime target looms large. Grey box testing comes up as a priceless tool for securing security in software. Significant vulnerabilities can be uncovered by giving in less effort and cost.
 Grey Box Testing Methodology
First – White Box Testing to study and gain a basic understanding of the internal features of the application.
Second – Design and define test cases based on thorough knowledge and understanding to cover each and every aspect of the application.
Third – Black box testing to execute developed test cases to externally test the qualities of the software application.
Best Suited Applications:
Grey-box testing is an ideal fit for Web-based applications.
Grey-box testing is the best technique for domain or functional testing
Grey Box Testing Strategy in software engineering
It's not necessary in this methodology that source code is required by the tester to design test cases. To carry out this testing process, test cases can be designed based on the algorithm, knowledge of architectures, internal states, or other advanced descriptions of the program behavior.
It utilizes all the clear-cut techniques of black box testing for function testing. The generation of a test case is based on requirements and presetting all the conditions by the assertion method.
The standard steps to carry out Grey box Testing are as follows:
Step 1: Selection and identification of inputs from White-Box and Black-Box testing inputs.
Step 2: Identification of probable outputs from the above-selected inputs.
Step 3: Identification of all the key paths to pass through during the testing phase.
Step 4: Identification of sub-functions to carry out deep-level testing.
Step 5: Identification of inputs for sub-functions.
Step 6: Identification of likely outputs for sub-functions.
Step 7: Execution of a test case for sub-functions.
Step 8: Verification of the appropriateness of outcome.
Step 9: Repetition of Steps 4 and 8.
Step 10: Repetition of Steps 7 and 8.
Security-related, GUI-related, Database related, Browser related, and Operational system-related testing are all part of the test cases designed for the process.
Types of Grey box testing/gray box testing/Grey box testing techniques
Matrix Testing
Matrix testing, a technique coming under Grey Box testing, defines all the used variables of a particular program. In any program, variables are the essential elements through which values can move through the program.
It should be on par with the requirement without which the readability of the program and speed of the software will be reduced. The matrix technique is a way to eliminate uninitialized and unused variables by identifying used variables from the program.
Examination of inherent risks like technical risks and business risks that are associated with the variables with different frequencies labeled by the software developer is carried out under this type of testing.
The design of test cases becomes smooth and easier when all of this information is summarized in two types of tables as in the following example:
Grey Box Testing Methodology
First – White Box Testing to study and gain a basic understanding of the internal features of the application.
Second – Design and define test cases based on thorough knowledge and understanding to cover each and every aspect of the application.
Third – Black box testing to execute developed test cases to externally test the qualities of the software application.
Best Suited Applications:
Grey-box testing is an ideal fit for Web-based applications.
Grey-box testing is the best technique for domain or functional testing
Grey Box Testing Strategy in software engineering
It's not necessary in this methodology that source code is required by the tester to design test cases. To carry out this testing process, test cases can be designed based on the algorithm, knowledge of architectures, internal states, or other advanced descriptions of the program behavior.
It utilizes all the clear-cut techniques of black box testing for function testing. The generation of a test case is based on requirements and presetting all the conditions by the assertion method.
The standard steps to carry out Grey box Testing are as follows:
Step 1: Selection and identification of inputs from White-Box and Black-Box testing inputs.
Step 2: Identification of probable outputs from the above-selected inputs.
Step 3: Identification of all the key paths to pass through during the testing phase.
Step 4: Identification of sub-functions to carry out deep-level testing.
Step 5: Identification of inputs for sub-functions.
Step 6: Identification of likely outputs for sub-functions.
Step 7: Execution of a test case for sub-functions.
Step 8: Verification of the appropriateness of outcome.
Step 9: Repetition of Steps 4 and 8.
Step 10: Repetition of Steps 7 and 8.
Security-related, GUI-related, Database related, Browser related, and Operational system-related testing are all part of the test cases designed for the process.
Types of Grey box testing/gray box testing/Grey box testing techniques
Matrix Testing
Matrix testing, a technique coming under Grey Box testing, defines all the used variables of a particular program. In any program, variables are the essential elements through which values can move through the program.
It should be on par with the requirement without which the readability of the program and speed of the software will be reduced. The matrix technique is a way to eliminate uninitialized and unused variables by identifying used variables from the program.
Examination of inherent risks like technical risks and business risks that are associated with the variables with different frequencies labeled by the software developer is carried out under this type of testing.
The design of test cases becomes smooth and easier when all of this information is summarized in two types of tables as in the following example:
 All Info About Grey Box Testing (With Examples)
From the information in the above two tables, the testing analyst can immediately make out that the technical and business aspect of the code, namely saving and deleting records requires testing.
Regression Testing
This type of testing is carried out after executing a functional development or repair to the program.
To verify whether the modification in any of the previous versions of the software has regressed or caused any unintended or adverse side effect in other aspects of the program in the new version, the following testing strategies can be pursued:
All Info About Grey Box Testing (With Examples)
From the information in the above two tables, the testing analyst can immediately make out that the technical and business aspect of the code, namely saving and deleting records requires testing.
Regression Testing
This type of testing is carried out after executing a functional development or repair to the program.
To verify whether the modification in any of the previous versions of the software has regressed or caused any unintended or adverse side effect in other aspects of the program in the new version, the following testing strategies can be pursued:
- Retesting within a firewall where dependencies are analyzed for choosing baseline tests
- Retesting risky use cases where the risk factor is considered
- Retesting all existing test cases
- Retesting by profile where time is allocated in proportion to the operational profile
- Retesting changed segment where code changes are compared for choosing baseline tests
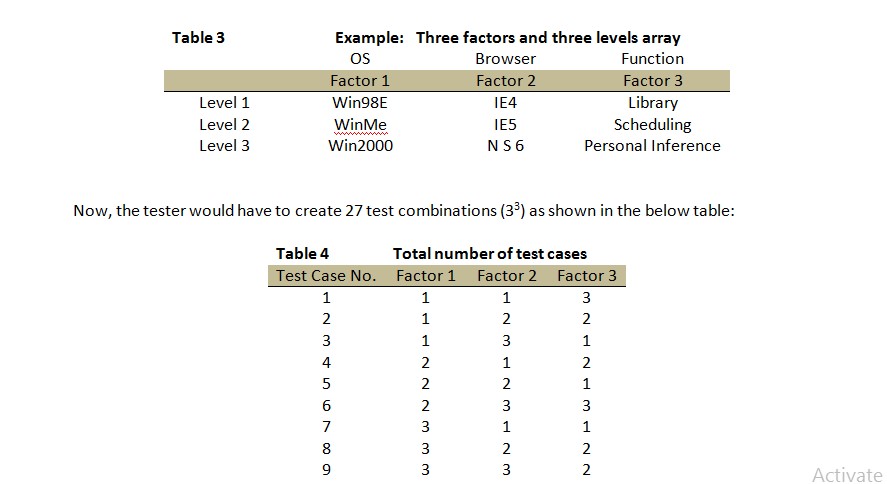 By conveying values for each factor and then, of course, extrapolating for combined pairing, the total number of test cases will surely come down to nine from 27.
Though simple, this effective technique helps in maximizing the required testing coverage.
Pattern Testing
This testing is carried out by using the record of analysis on the historical data of the previous system defects. These analyses may contain specific reasons for the defect or bug with information on the problem that has been addressed, applicable situation, generic test cases, etc.
Unlike black box testing, grey box testing plows within the code to determine the reason for the failure so that they can be fixed in the next software. It is noteworthy that pattern testing is applicable only to such type of software that has been developed by following the same pattern of previous software as the possibility of similar defects occurs in this software only.
Generally, the Grey box methodology employs automated software testing tools to conduct the testing. Module drivers and stubs are created to relieve the tester from manually generating the code.
Examples for grey/gray box testing
Grey Box Testing is said to be performed when –
By conveying values for each factor and then, of course, extrapolating for combined pairing, the total number of test cases will surely come down to nine from 27.
Though simple, this effective technique helps in maximizing the required testing coverage.
Pattern Testing
This testing is carried out by using the record of analysis on the historical data of the previous system defects. These analyses may contain specific reasons for the defect or bug with information on the problem that has been addressed, applicable situation, generic test cases, etc.
Unlike black box testing, grey box testing plows within the code to determine the reason for the failure so that they can be fixed in the next software. It is noteworthy that pattern testing is applicable only to such type of software that has been developed by following the same pattern of previous software as the possibility of similar defects occurs in this software only.
Generally, the Grey box methodology employs automated software testing tools to conduct the testing. Module drivers and stubs are created to relieve the tester from manually generating the code.
Examples for grey/gray box testing
Grey Box Testing is said to be performed when –
- The codes for two modules or units are studied for designing test cases which is the White Box Testing method and then
- Actual tests are conducted using the exposed interfaces which are the Black Box Testing method.
 Objectives of Grey Box Testing
Some of the main objectives are:
Objectives of Grey Box Testing
Some of the main objectives are:
- To help combine the inputs from both testers and developers to get the best results
- To improve the overall quality of the product with less cost
- To find defects early and get the developers more time to fix the issues
- To combine the advantages of both black box and white box testing
- To reduce the overhead of functional and non-functional test documentations
- The testing is carried out from a user perspective and hence helps to improve the overall quality of the application.
- In most cases, the testers do not need technical or programming knowledge to get started with grey box testing. This also means that the manual and automation testers can both perform this testing with equal ease.
- Since the defects are found earlier, it gives the development teams more time to fix and deploy the changes.
- The clarity and transparency of the test ensure there are no conflicts between the testers and developers.
- It can be much more effective both quality-wise and cost-wise when compared to integration testing
- Since we are looking at only part of the system, it is very difficult to assign defects to a particular module.
- Since the testers have only limited access to the code, they have only limited knowledge about the paths traversed. This can reduce the coverage.
- It can be difficult to design effective test cases for grey box testing
- It can not be used for algorithm testing
- Neither white box nor black box testing benefits can be reaped fully through the process.
- In some cases, the test case may be a pass but the displayed results would be incorrect. Such cases can not be handled well in grey box testing.
- In case the module under test crashes it may lead to aborting the test and it would be difficult to find the reason.
- Testers do not have access to the source code, hence they may miss some critical vulnerabilities in the application
- For large applications, it can be very time-consuming to check all the input combinations and traverse all the different paths involved.
- Selenium
- Appium
- Postman
- Chrome Dev Tools
- Burp Suite
- JUnit
- Cucumber
- RestAssured
 Conclusion
Nowadays in this modern world, nobody is indisputably safe from cybercrime irrespective of whether it is a big corporate or an individual, government organization, or non-benefit association.
The potentiality of becoming a cybercrime target looms large. Grey box testing comes up as a priceless tool for securing security in software. Significant vulnerabilities can be uncovered by giving in less effort and cost.
Conclusion
Nowadays in this modern world, nobody is indisputably safe from cybercrime irrespective of whether it is a big corporate or an individual, government organization, or non-benefit association.
The potentiality of becoming a cybercrime target looms large. Grey box testing comes up as a priceless tool for securing security in software. Significant vulnerabilities can be uncovered by giving in less effort and cost.

 Mobile App Testing
Mobile App Testing Web App Testing
Web App Testing Game Testing
Game Testing Automation Testing
Automation Testing Security Testing
Security Testing Performance Testing
Performance Testing Selenium
Selenium Test Management
Test Management Usability Testing
Usability Testing Guides and Tutorials
Guides and Tutorials Expert Insights
Expert Insights Software Testing Events
Software Testing Events Load Testing
Load Testing Performance Testing
Performance Testing Hire a Tester
Hire a Tester





